7 cybersecurity summer travel tips

7 cybersecurity summer travel tips
After our practical and general checklist to prepare for your holiday, you are probably already figuring out your flight, hotel, good restaurants, places of interest, and so on. Or maybe you are already enjoying your well-deserved rest. In this article we provide you with tips to keep it safe – at least in terms of cybersecurity – on vacation.
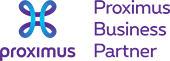
1. Don’t get caught out by phishing.
Even though it is summer, cyber criminals remain active and a phishing attack is always possible. If you receive a suspicious email or text about an urgent password change or a payment to a supplier that can’t wait, or anything else strange and suspicious, beware! Even if the message is from a known contact, it could be phishing. In such a case, check the sender’s address and, above all, never share passwords or other sensitive information in response to such an email. When in doubt, you can of course contact K-Force.
Did you know that you can teach yourself and your employees to better recognize phishing? We have a great solution for this, which will test and train you and your employees. After all, phishing isn’t about computers, it’s about people. Despite all (much-needed) IT security, it is often an employee who clicks on a wrong link, opens an unsafe attachment or worse, enters payment or login details on a rogue website.
2. Be careful with public Wi-Fi.

Image author: Startpage
Many hotels, airports, B&Bs, etc. provide public WiFi networks. These are often networks without passwords and without security. It goes without saying that we strongly advise NOT to use them, especially if you are working with sensitive data, such as payments. Always try to use a secured network with a password, alternatively use your mobile data network.
On the other hand, teleworking has become commonplace, and there are ways to securely connect to such a public Wi-Fi. In the first place, it is important that your device has good endpoint protection (antivirus, anti-malware, host firewall, etc.). Also, always use a VPN to encrypt your connection, so that others on such a public network cannot intercept your email or other data. If you want to connect to our full cloud solution, this is a secured and safe connection, even on a public network.
3. Only download trustworthy apps.
In your spare time, you may want to download a game or an app to edit your vacation photos and videos. Malicious apps have access to all data on your phone, including company data. If you want to download an application, please only do so through the official Apple or Google stores on mobile devices. For computers only use the Microsoft or Apple stores.
4. Protect your identity.
Provide as little (personal) information as possible with purchases, forms, etc. Do not hesitate to ask what the requested information will be used for. Is a scan of your passport or credit card really necessary? Do people really have to write down your credit card number, expiry date and security code (CVV number) after a successful payment?

Photo by Jason Dent on Unsplash
5. Resist the urge to share (too much) on social media.

The less detail we share online about our vacation, the better. Such as where you are and for how long. Always keep in mind that any uploaded information can be used in unexpected ways. Physical burglars can use this information to rob your home, but social engineers can also use it to craft an even better spear phishing email that can lead to a cyber attack.
6. Be careful what you connect to your computer.
USB infections are still common despite it being an old hacking technique. Avoid plugging in USB sticks on your computer.
7. Use multi-factor authentication whenever you can.
Hackers have many ways to steal your passwords. Maybe they got it from you through phishing. Maybe they hacked into a site you have an account on. If you use the same password for other accounts, this is a problem. MFA can still save you if the hacker knows your password! Because every time someone tries to log in with your account, they also need a second identification, such as the approval of a notification on your smartphone. This makes it much more difficult to hack your accounts. In addition, you will be warned with every login attempt. So always activate it if you are given the choice for your personal accounts. For example, the most well-known platforms such as Facebook, LinkedIn, Instagram, etc. offer the option for free.
In addition, opt for a professional solution for your business accesses. We can of course assist you with this.
All that remains is for us to wish you a pleasant and above all carefree holiday! As always, you can contact our helpdesk in the event that you are faced with an IT challenge. ?
Article in collaboration with WatchGuard security solutions. K-Force is a certified WatchGuard partner and assists SMEs on a daily basis with regard to security.
Our team of account managers is ready to help you

Christian

Jordan

Jurgen
Didier

Jean-Marc

Kaj